Read time: 5 minutes
Ransomware is a malware attack that encrypts your files. It can lock your images, videos, documents, SQL database files, and other important data files. The attacker demands a ransom amount to remove the encryption. One popular example is WannaCry, the ransomware that affected millions of computers worldwide in 2017.
When your MDF files become inaccessible after a cyberattack, you are left with two choices. You can either pay the ransom (which does not guarantee data safety) or recover the data on your own. The best method to recover MDF files after ransomware attack is using the SQL backup file.
Working Method to Recover MDF Files After Ransomware Attack
We will use the SQL Server Management Studio for MDF recovery. Step-by-step process is given below:
Step 1: Open the SSMS tool and connect to the SQL Server.
Step 2: In the Object Explorer tab, select and right-click Databases. Then, select the option Restore Database.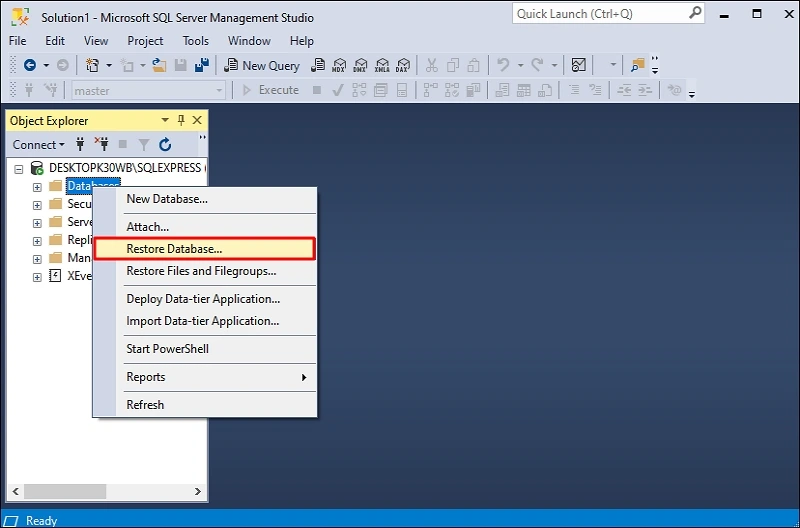
Step 3: In the source section, select Device and click on the browse button. Then, in the Select backup devices window, click the Add button.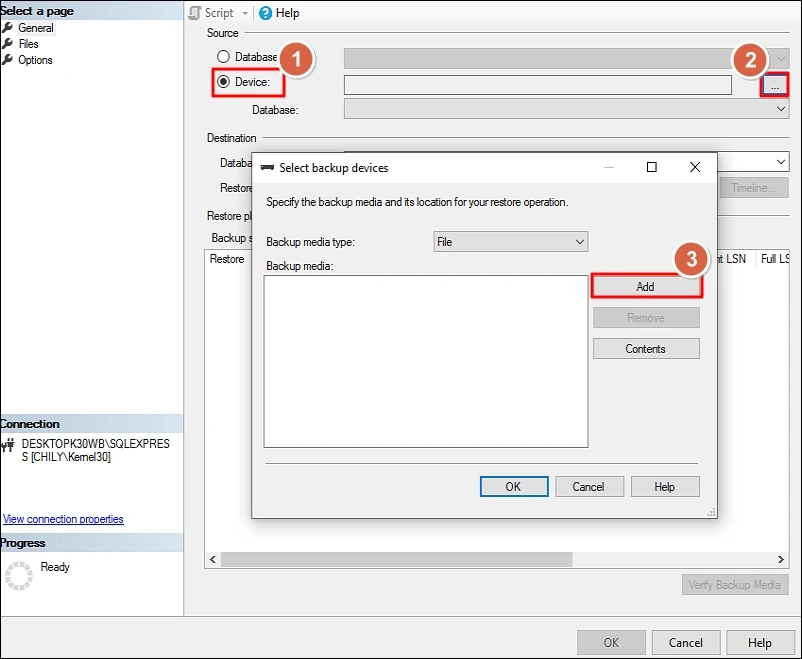
Step 4: Go to the location where the database .bak file is stored. Select the backup file and click OK to go back to the Select backup devices window. Again, click OK.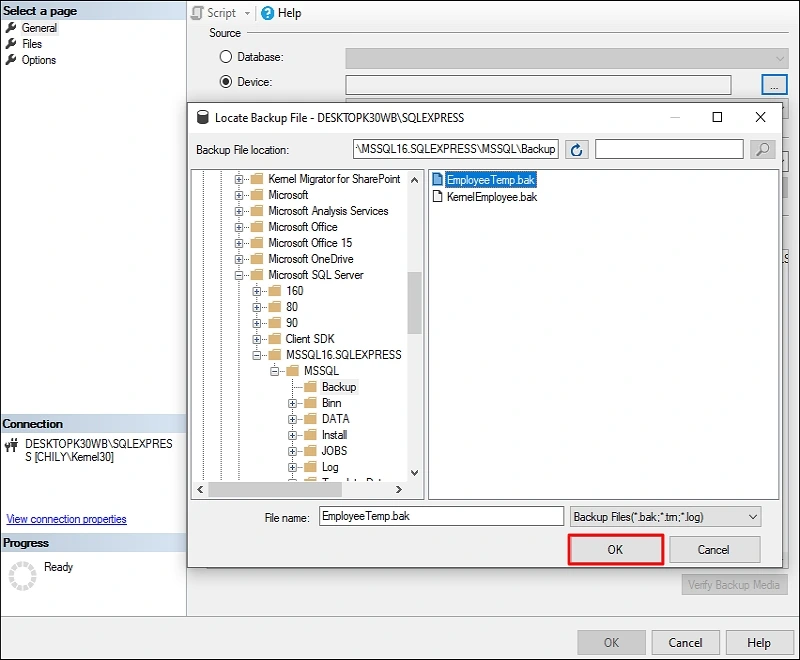
Step 5: Selected .bak file is added as the source. Now, on the left-side pane, click the option Options under the Select a page tab.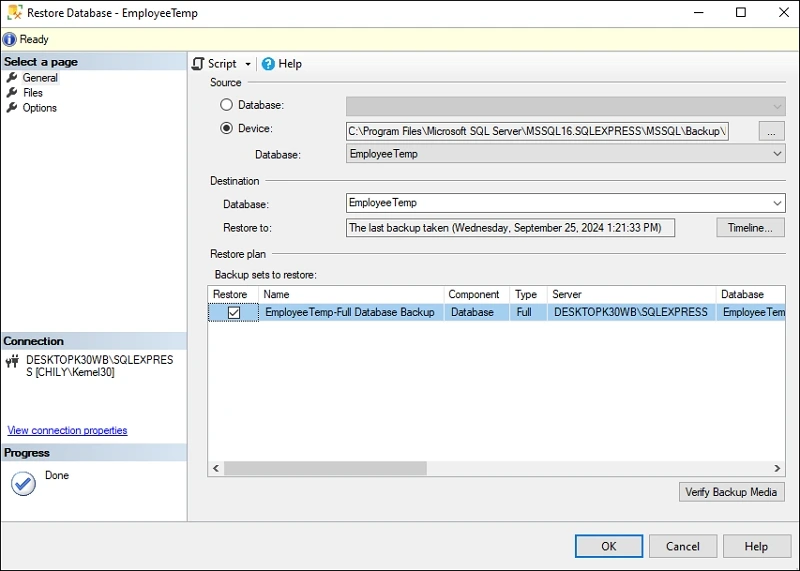
Step 6: You can modify or set different conditions for restoring SQL database. Configure the restoration as per your requirements. Click OK to restore MDF file.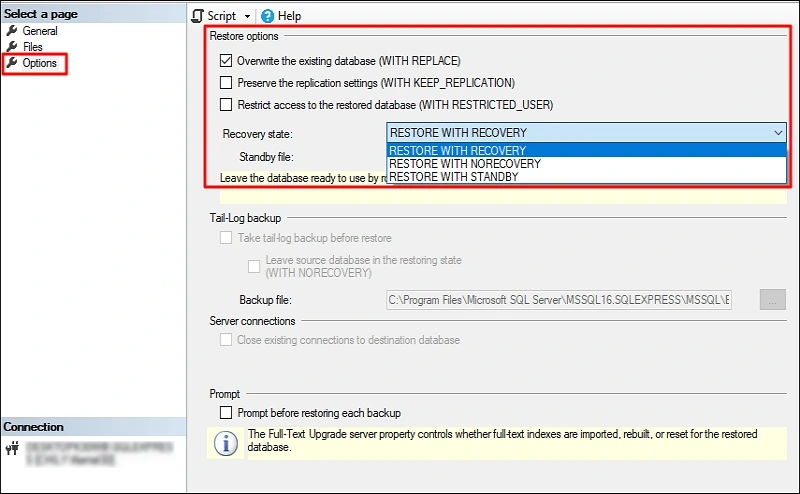
Step 7: You will receive a confirmation message after a successful MDF recovery.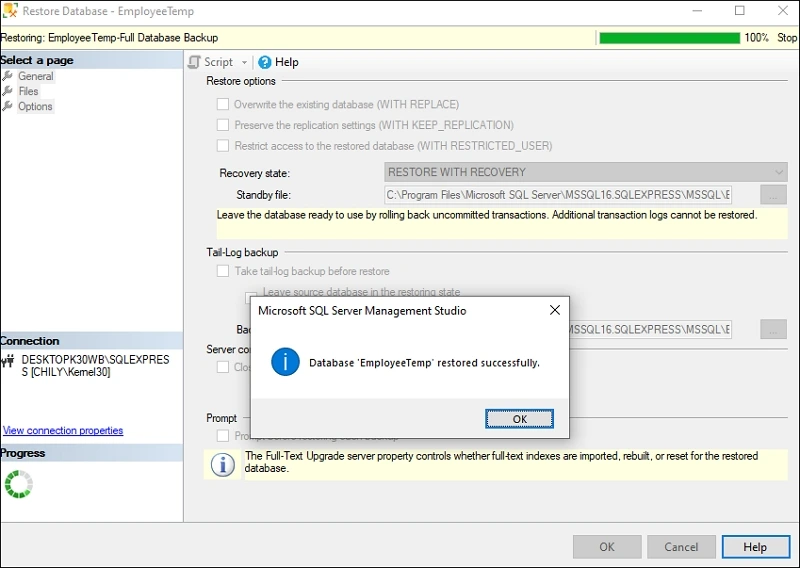
If you have multiple databases for restoration, follow the exact steps above to restore SQL database. If you have technical expertise with SQL commands, you may use a quicker way to recover MDF files after ransomware attack. Using T-SQL RESTORE query, you can restore MDF file from BAK file easily. T-SQL command to restore the database is given below:
The ransomware is broadly categorized into several types:
FROM DISK = ‘database-bak-file-complete-path”;
Note: MDF file recovery using a backup file will only restore the data to the point when the backup file was created. Any data added to the database after the creation of the backup file will not be recovered.
Preventive Measures from Ransomware Attacks
To safeguard your MDF, LDF, and NDF files from a ransomware attack, implement the following points.
Database Backup
Backing up your database is the ultimate solution for fast MDF file recovery. A robust and consistent backup allows to easily recover MDF files after ransomware attack. Take Full, Differential, and Transaction Log backup frequently. Make three copies of your data and store them on different devices. Keep at least one backup copy off-site (offline and outside organization storage)
Regular System Updates
Ransomware attacks target not only the SQL database but the complete system. Keep your operating system (Windows, MacOS, Linux, etc.) up to date with the latest security patch installed. Turn on the automatic updates to skip manual updating.
Install Powerful Antivirus
Anti-malware software is the first line of defense against any ransomware attacks. Invest in a capable antivirus tool that can protect you from offline as well as online threats. Do not download and install software from unknown or untrusted sources. Whenever you attach a storage device to your system always run a complete scan on the device.
Training and Awareness
Make your teammates or employees aware of the potential risk of opening any unknown link. Ask them not to run any script whose origin is not known. Train them to securely handle different forms of cyberattacks like phishing, social engineering, etc.
How to Restore a Corrupt Database?
Using the SQL Server Management Studio and a healthy backup file you can recover MDF files after ransomware attack. But what will you do if the database after recovery becomes corrupt. Such a situation can arise if the backup file you used for MDF recovery was damaged, has inconsistent data, or misses log files.
To restore MDF files from corruption you will need a third-party SQL database recovery tool. Kernel for SQL Database Recovery is an advanced tool designed with the help of SQL experts. Recover complete database objects with 100% data integrity using the powerful algorithms embedded in the tool.
Conclusion
With a healthy database backup file, you can recover MDF files after ransomware attack without paying a single penny. To prevent ransomware cyberattacks in future, strengthen your security with the preventive measures discussed in this blog. In case your recovered database is corrupt or inaccessible, use Kernel for SQL Database Recovery. The SQL database repair tool helps users to quickly recover complete database without any data loss.