Read time: 5 minutes
Multi-factor Authentication (MFA) is an immense cloud and data security innovation. It provides a new security layer to the existing infrastructure, enabling you to protect your information against all odds. Many cloud-based applications like Google, Yahoo, and Microsoft already provide this feature in most of their applications.
Last year, Microsoft released two new features to improve MFA for Azure AD accounts to work better and faster. These new features offer enhanced security, provide protection data against all loopholes and attacks and help come out of Office 365 messages stuck in Outlook state and other similar problems.
What’s new with MFA?
With a few minutes, any administrator can quickly improve user security using these new features- Number Matching and Additional Context in Multi-factor Authentication.
- Number Matching
This mechanism is used for password-less authentication. It is the process of double identification. It allows users to enter the exact number from the sign-in screen to the application; only then the authentication will be approved. - Additional Context
This feature means the Authenticator app will display extra information while requesting an authentication. At this point, two pieces of information will appear on the screen, including the authentication request and their sign-in location depending on the device’s IP address.The device IP address accuracy depends on various factors, but it’s good to have the assurance that the sign-in effort is not from somewhere impossible. For example, if you want to add a shared mailbox in outlook, then the MFA will make sure that no unauthorized user can access it. Additional context combines the sign-in with number matching to give users enough information to understand a complete authentication context.
How to update additional context and number matching via Azure AD Admin Center?
In Azure AD settings, you can easily enable additional context and number matching for Authenticator. To do so, follow the below steps:
- Go to the Authenticator methods blade in the settings.
- Select Microsoft Authenticator from the menu, and click the “…” option right under Target to reveal the Configure fly-out.
- Set the value of both the parameters to Show additional context in notifications and Enabled.
Both features will be labeled Preview, and they’ll be available shortly.
How to Update the Authenticator Configuration with the Graph Explorer?
Graph Explorer is an alternative option to Azure AD to configure the two features. However, this method is a little more complicated than Azure AD settings.
The Graph API allows you to run multiple queries while underpinning many parts of Microsoft 365. Even if you don’t have Graph API experience, you can still run commands via Graph Explorer to understand how queries work and what they return.
To use Graph Explorer, follow the below steps:
- Open Graph Explorer on your system and sign in with a tenant administrator account.
- Now, add the below query into the command box while choosing the beta endpoint, and click Run.
- After running this command, you might get an error because Graph Explorer doesn’t have permission to access the Authenticator configuration.
- Click Modify Permissions and select Open the permissions panel link to choose Policy.ReadWrite.AutheticationMethod from the set of Graph permissions.
- Click Consent, and you’ll find the normal permissions requested dialog to grant the request.
- After that, accept the consent request and return to the Graph Explorer.
- Now, rerun the query again with the Graph Explorer having the necessary permission. Furthermore, you’ll find the current configuration in the response box.
- Copy the JSON-formatted output and paste that text into the request body.
- Now, modify the Number Matching Required State value and Display App Information Required State properties to enable.
- The Graph Explorer will start running queries by default to return information if you want to update the setting, select PATCH from the drop-down query type list.
- Click Run query to make the change to see the response.
https://graph.microsoft.com/beta/authenticationMethodsPolicy/authenticationMethodConfigurations/MicrosoftAuthenticator
Note: Make sure you don’t change the formatting or structure of the request body.
After that, you can validate the configuration settings by changing the query type to GET and un the query to see the current configuration.
How to Limit Features to a Specific Group?
Anyone can use the above methods to enable number matching. But, you can limit this feature to a specific group or individuals to enhance MFA. To do that, you need to change the Id property from “all_users” to the object identifier of an Azure AD group.
To find the group identifier, you can check the Azure AD admin center and copy the identifier from the group properties.
Backup Microsoft 365 Data for Better Security
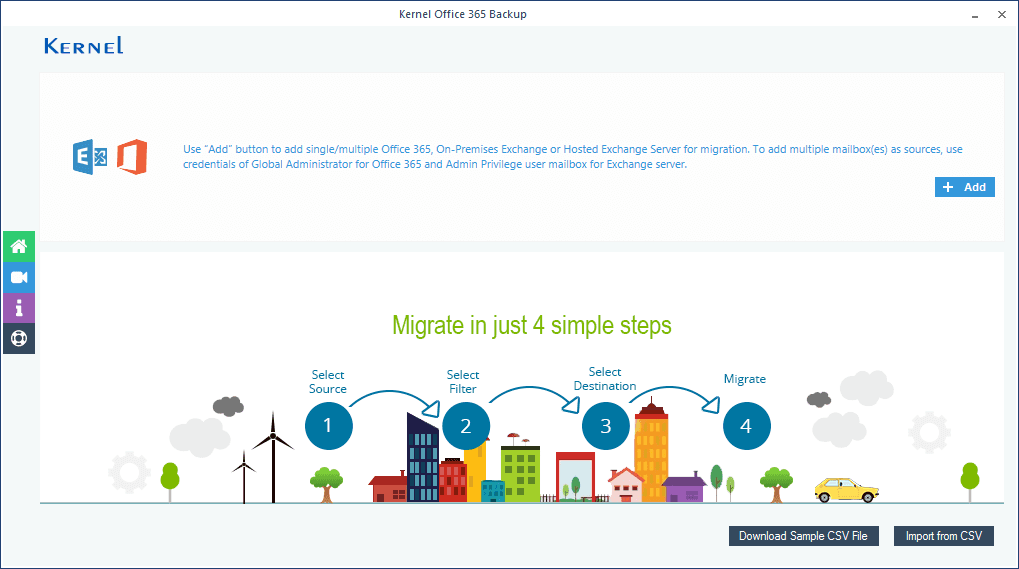
If you find it complicated to use the above methods to enhance MFA in Microsoft 365, you can backup your entire data and save it on your local system. However, to take the backup of the whole data manually would be a time-consuming and lengthy process. So, the best solution is to use an automated tool like Kernel Export Office 365 to PST, which allows you to backup entire data quickly with a simple approach.
It is designed to help you backup Office 365 mailbox data to PST and different formats. It provides two options – Basic Authentication & Modern Authentication – which ensure safe and hassle-free Office login in all situations. Modern Authentication uses 2-factor or multi-factor Authentication and assures the complete security of Office 365 data. The tool is equipped with advanced filters that enable users to backup specific data based on various parameters like date, to, from, type, etc. The tool is available as a trial version for users to help them understand the tool’s functionality.
Final Words
Microsoft is continuously improving the security of Office 365 data with enhanced multi-factor authentication with an Authentication app. However, it is still confusing why most Microsoft tenants don’t use MFA to protect users. There is no doubt that MFA provides users with additional security and allows users to secure Microsoft 365 data. This article highlights how you can enhance MFA with number matching and additional context features.