Read time 4 minutes
It is a great challenge for organizations to protect their data as it is vulnerable in different ways. Data is not always secure, and many threats are looming from random sources. It is the responsibility and need of the businesses to adopt some protection measures to guard their data.
Here, we will be discussing some threats and risks to the system data and measures which could be adopted for safeguarding it.
Use passwords
If the system is not protected, then any random person can access it and steal or manipulate data on your system in your absence. Similarly, some vital software also requires protection to avoid misuse. But sharing passwords to many could also turn out as a risk.
Recommended Measures
- Protect user accounts by assigning strong passwords.
- Passwords should be long and a combination of alphabets, numerals, and symbols.
- The software applications can be protected by assigning passwords to them.
- Avoid sharing your password to anyone.
Update software
System software or applications, if not updated for a long-time, lack new features and bug-fixes. Every new update to the software incorporates new features to improve data security. But if you are not concerned about the updates, it becomes easy for hackers to steal the data from the unpatched system software.
Recommended Measures
- Always turn on automatic update for system Windows. It will keep all Windows and Microsoft tools updated.
- Turn on automatic updates for other applications like anti-viruses, firewall, and browsers.
- Turn on the notifications for any recent update available for all frequently used applications.
Back up regularly
System data can be restored even after the crash of the hard disk, corruptions in disk partitions, etc., if the user is in a regular practice of keeping a secure backup at an external place. Otherwise, users can lose data permanently in such situations.
Recommended Measures
- Configure automatic backup of the critical data.
- Do backups at regular frequent intervals – either manually or automatically.
- Try keeping crucial data at a safer location like on external devices like external hard disk, CD, etc.
Use anti-virus
Your data is always under the risk of attacks from viruses, malware, spyware, bugs, etc., which would ultimately corrupt or steal your data. Viruses can enter your system through malicious links, foreign emails, external devices, etc.
Recommended Measures
- Try installing the best & genuine anti-virus, anti-spyware, firewall on your system.
- Turn on the notifications in the anti-virus scanner for pre-alerts and warnings for any threat.
- Keep the installed antivirus or anti-spyware always ON for automatic regular updates.
Use genuine software
Malicious software can enter your system from different sources like untrusted websites, software download links, fake advertisements or ingenuine message pop-ups. Many times, users get duped by fake software download sites or program links that install many malwares on their systems.
Recommended Measures
- Use secure web browsers like Firefox, Chrome or Microsoft Edge which has the features to identify and block malicious websites.
- Avoid direct opening of suspicious links or attachments online or in emails without any personal verification.
- Always use trusted and genuine sources for downloading any software program.
Monitor Computers
There are chances of data breach by employees working in the organization. It can be transferring of files, accidental or intentional deletion, data manipulation, leaking of business secrets or financial details for personal profits, and data theft from PC through external devices like Pen Drive, External Hard Disk, CD, DVD, etc.
Recommended Measures
- Train the employees on how to manage their data securely.
- Take regular backups of crucial system data of all employees in the organization.
- Block access to the websites not related to the work.
- Safeguard data by keeping an eye on physical devices.
- Install a reliable Employee Computer Monitoring tool.
For monitoring the employee activities on a system, taking help from software would be recommended rather than manual supervision. There are many benefits for Employee Computer Monitoring tool, like automatic supervision, tracking from a central location, etc.
While talking about a reliable Employee Desktop Monitoring tool, we introduce you the efficient Kernel Employee Desktop Live Viewer tool.
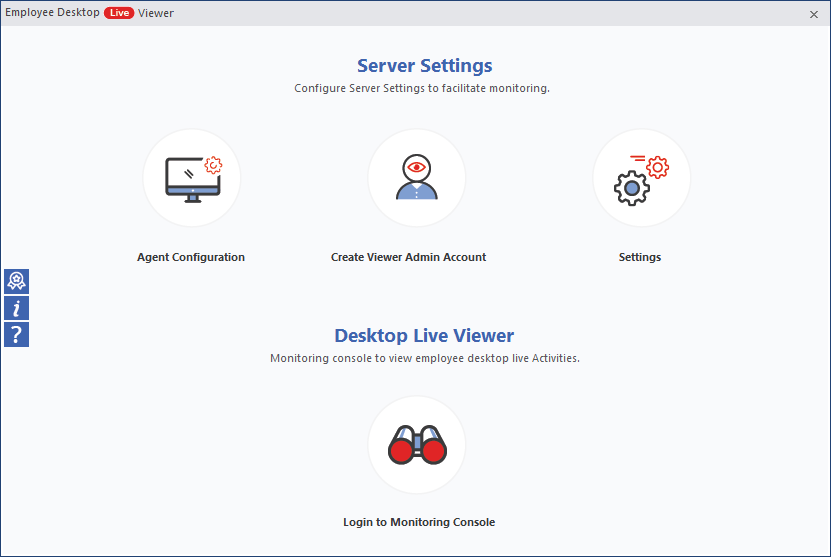
The important features of this Employee desktop monitoring tool are:
- Performs monitoring without employees’ knowledge
- Delivers uninterrupted monitoring while the system is ON
- Facility of dual screen monitoring
- Can monitor the desired number of computer systems
- Allows search and download monitoring videos
This advanced tool also helps organizations to increase an employee’s productivity. You can find its advantages by running its absolutely free Trial version available on the website.
Conclusion
The security of data on their systems is important for organizations. Several basic techniques, including employee system monitoring, could be adopted for protecting the data on computers. And using an employee monitoring tool is a is a popular way to surveil the employees’ computer activities and eliminate data thefts and security breaches.




